Every Game Hacking Technique Explained. Ready to unlock your gaming potential? In this explosive video, “Every Game Hacking Technique Explained,” we dive deep into the world of gaming hacks.
From speed hacks to aimbots, we reveal ALL the secret techniques that can give you the upper hand! Whether you're a newbie or a seasoned pro, learn how some top players bend the rules for victories.
Get ready for insider tips, practical demos, and the ethics of hacking gaming! Don’t miss out on transforming your gameplay strategy! Hit that subscribe button and join our gaming revolution! ⏰ #GameHacking #GamingTechniques #GamerLife
Show More Show Less View Video Transcript
0:00
today I'm going to go in depth into
0:01
every video game hacking technique out
0:03
there this video is perfect for
0:04
beginners getting into game hacking or
0:06
just anyone wanting to learn all the
0:08
known methods of bypassing anti-cheats
0:10
in depth this is policy point and don't
0:11
forget to subscribe so let's begin with
0:13
a basic overview of game hacking game
0:15
hacking is all about exploiting a game's
0:17
weaknesses to gain unfair advantages
0:19
like using cheats for extra abilities or
0:21
automating actions hackers constantly
0:24
find new ways to bypass anti-che systems
0:26
while developers work to block them in
0:28
this video I'm going to be breaking down
0:30
the key techniques used in this ongoing
0:31
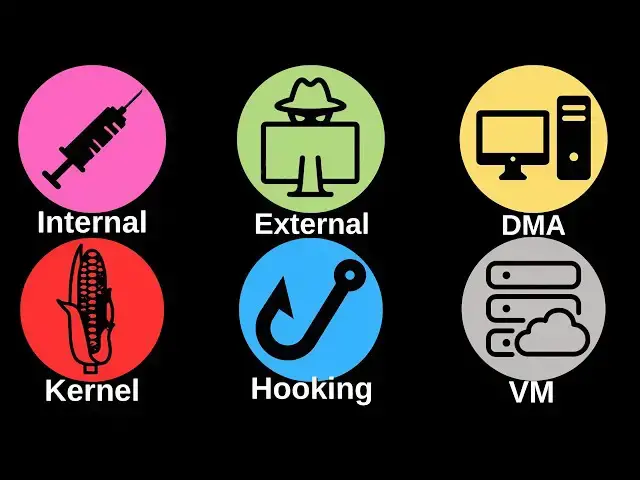
battle the number one and most powerful
0:33
method of game hacking is internal
0:35
cheats internal cheats are programs or
0:37
code that are injected directly into a
0:39
game's process since they are part of
0:41
the game's memory space they have full
0:42
control over everything the game does
0:44
this is incredibly powerful because the
0:46
key acts like a native part of the game
0:48
allowing it to bypass certain
0:50
restrictions to inject an internal cheat
0:52
a method called DL injection is used as
0:55
a doll Dynamic link library is a file
0:58
that contains code and data that can be
0:59
used used by multiple programs at the
1:01
same time the injection process involves
1:03
loading the dll into the game's memory
1:05
granting the cheat access to the game's
1:07
internal functions however anti-cheats
1:09
can detect this by monitoring the loaded
1:11
modules for instance if a game finds a
1:14
module in memory that doesn't belong
1:15
like a dll cheat it Flags it as
1:17
suspicious games like csgo have even
1:20
blocked all doll injections hackers
1:22
responded by using methods like manual
1:24
mapping which emulates the dll loading
1:26
process but avoids being listed in the
1:28
game's loaded modules making detection
1:30
harder the number two method is external
1:33
cheats external cheats run separately
1:35
from the game but still manipulate the
1:36
game's memory this method doesn't
1:38
directly alter the game's process making
1:40
it less detectable external cheats
1:42
interact with the game's memory by
1:44
opening a handle to the game process
1:46
using Windows API functions like read
1:48
process memory and WR process memory
1:51
these functions allow the key to read
1:52
from and modify the game's memory
1:54
without being a part of the game however
1:56
external cheats have their challenges
1:58
external cheats are easier to detect
2:00
because they rely on common Windows
2:02
functions user mode anti-cheats which
2:04
don't have deep system privileges often
2:06
block external Cheats by hooking these
2:08
API functions for example they hook open
2:11
processes to prevent cheats from getting
2:13
access to the game's memory in the first
2:15
place the number three method is dmab
2:17
based cheats dmab based cheats use
2:20
external hardware devices to access game
2:22
memory directly without involving the
2:24
CPU or operating system this makes it
2:26
extremely hard for software-based
2:28
anti-cheats to detect EMA is a
2:30
technology that allows peripherals like
2:32
network cards to communicate directly
2:34
with the system's memory bypassing the
2:36
CPU dma cheats use the same principle a
2:39
hardware device is plugged into the
2:41
computer's pcie slot and then connected
2:43
to a separate computer the second
2:45
computer can directly read and write the
2:47
game's memory without any cheat software
2:49
running on the actual PC itself since no
2:51
cheat software is running on the gaming
2:53
computer traditional anti-cheats can't
2:55
detect it however dma cheats require
2:58
expensive hardware and a second computer
3:00
to run the hack making it less
3:01
accessible to Casual hackers method
3:03
number four is hooking hooking refers to
3:05
modifying or intercepting API calls or
3:08
game functions to control or alter their
3:10
behavior it's a common technique used by
3:12
both cheats and by anti-cheats hackers
3:14
use hooking to override certain game or
3:16
system functions for example a cheat
3:18
might hook the game's rendering function
3:20
to create an ESP overlay showing the
3:22
player where enemies are anti cheets
3:24
also use hooking but in Reverse they
3:26
hook critical Windows functions like
3:28
load Library which is is used to inject
3:30
dlls or open process which is used to
3:33
manipulate memory preventing cheats from
3:35
using these functions to gain access to
3:37
the game one way to bypass anti-che
3:39
hooks is by not using the hooked
3:41
functions at all techniques like manual
3:43
mapping avoid the need for load Library
3:46
making it harder for the anti-che to
3:47
block the cheat the number five method
3:49
is Kernel level cheats kernel level
3:51
cheats typically use custom drivers or
3:53
exploit vulnerabilities in existing
3:55
drivers to execute their code in kernel
3:57
mode the key installs a malicious driver
3:59
that interacts directly with the game's
4:01
process memory or even Hardware making
4:04
it much harder for user level anti-che
4:06
programs to detect once running at this
4:08
level cheat has full access to read and
4:10
write memory and manipulate input
4:12
devices for example simulating Mouse
4:14
movements for Aimbot and modifying
4:15
critical game functions without raising
4:17
alarms some kernel level cheats are so
4:19
Advanced that they can hide themselves
4:21
in processes they can mask their
4:23
presence from anti-che programs by
4:25
controlling what processes are visible
4:27
at the user level thus making detection
4:29
much more challenging you can also load
4:31
a custom or compromised driver in the
4:33
key and can gain access to the game's
4:35
memory and resources via the driver
4:37
kernel level cheats don't come without
4:39
their challenges though modern anti-che
4:41
systems are increasingly moving to
4:43
Kernel level detection themselves like
4:45
riots Vanguard or easy anti making this
4:47
method much more difficult to pull off
4:49
loading unsigned drivers are improperly
4:52
written code can also lead to system
4:54
instability and crashes hackers may need
4:56
to exploit vulnerabilities in the
4:58
operating system or hard W successfully
5:00
install and run their drivers without
5:02
triggering detection mechanisms the
5:04
sixth and probably least common method
5:06
is the virtual machine-based cheat a
5:09
virtual machine-based cheat uses
5:11
hardware virtualization to create an
5:13
isolated environment where the game runs
5:15
inside a virtual machine while the cheat
5:17
runs outside in the host System since
5:19
the cheat operates outside the
5:21
virtualized environment it can monitor
5:23
and manipulate the game without ever
5:24
directly interacting with the game's
5:26
process or memory from within the guest
5:28
OS making it ult for anti-che systems to
5:31
detect a hypervisor is used to run the
5:33
game inside a virtual machine this
5:35
hypervisor has full control over the
5:37
virtual machine's memory and CPU State
5:39
the key can then read the memory of the
5:41
VM extracting useful information like
5:43
player locations or in-game variables by
5:46
staying outside the virtualized
5:47
environment the cheat remains hidden
5:49
from user mode anti-che software running
5:51
inside the VM like the other methods
5:53
this doesn't come without its challenges
5:55
setting up a VM based cheat requires
5:57
knowledge of virtualization Technologies
5:59
and hypervisor programming there is also
6:01
a performance overhead when running
6:02
games inside virtual machines although
6:04
Hardware assisted virtualization like
6:06
Intel or AMD helps mitigate this
6:09
furthermore some anti-che systems are
6:11
starting to detect when games are run
6:12
inside virtual machines flagging this as
6:15
suspicious please like And subscribe to
6:16
policy point if you enjoyed the video
6:18
I'm going to be making more videos like
6:20
this in the future and teaching you guys
6:21
how to actually make these so stay
6:23
subscribed bye for now
#Computer Security
#Hacking & Cracking
#Computer & Video Games
#Fighting Games
#Sandbox Games
#Video Game Emulation
#Competitive Video Gaming