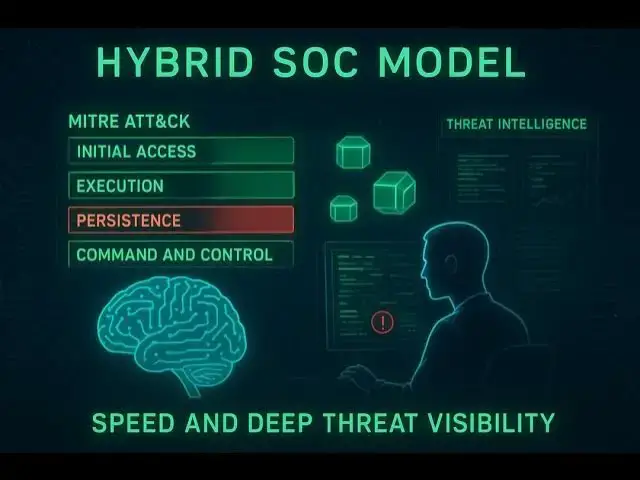
Cyber threats are evolving at an unprecedented pace, with sophisticated ransomware and supply chain breaches on the rise, contributing to cybercrime costs estimated to exceed $10.5 trillion per year by 2025. We delve into the optimal hybrid SOC model, discussing how organizations leverage AI-driven automation to reduce Mean Time to Detect (MTTD) by up to 40% and align defenses using the MITRE ATT&CK framework. Learn why critical gaps in lateral movement and impact detection, coupled with underfunding training (only 20% of SOC budgets), remain persistent challenges that security leaders must address to transition from reactive to predictive defense.
https://cisomarketplace.services/ciso-calendar
https://www.scamwatchhq.com/scammer-calendar-a-year-round-guide-to-scams-and-their-peak-times
Show More Show Less View Video Transcript
0:00
Welcome to the deep dive. We are uh closing out cyber security awareness month here in October 2025.
0:07
And if you like well like a lot of security folks feel like the threat landscape is just evolving faster than
0:13
ever before, you're definitely not wrong. The pace, the complexity of attacks, it's reached a point that's
0:20
frankly unprecedented. Yeah, it really has. It's not just a feeling either. The data, you know, it
0:25
supports this speed up. We're looking at figures showing a pretty dramatic increase in well targeted aggression.
0:32
For instance, ransomware attacks aimed specifically at industrial operators. You know, the companies running our critical infrastructure, they surged by
0:38
a massive 46% in just the first quarter of this year. 46%. Wow. That's that's basically an
0:44
operational nightmare unfolding in real time, isn't it? And we've seen how quickly these attacks can just lead to catastrophic failure. We've looked at
0:51
breaches this year. I mean, remember those two major UK businesses that resulted in 6.5 million people having
0:56
their data stolen? O yeah. And the collateral damage is often well often worse than the initial
1:02
breach itself. Look at that case. The 158-year-old UK firm KMP Logistics. They
1:07
ceased operations entirely, put 700 people out of work, all because the Akira ransomware gang exploited a single
1:14
weak password. A single password. That's just it sums up the whole strategic challenge facing
1:20
well every organization right now, doesn't it? The threat isn't always some super sophisticated zero day thing.
1:25
Often it's a failure of like basic hygiene, but amplified by a really organized cyber crash.
1:31
Exactly. And that's why our mission today is really tailored for you, the listener. We're taking this um this overwhelming flood of facts and stats
1:37
and trying to distill it into clear, actionable, strategic insights. We're focusing on what you need to know right
1:43
now to plan proactively for 2026. Okay, so we're going to unpack the most dangerous trends of 2025 ransomware,
1:49
social engineering, the uh the devastating cost of security debt. Then we'll explore the emerging strategic
1:55
dangers, things like the AI arms race, and um the escalating requirements of global compliance frameworks like zero
2:01
trust and CMMC, right? And just to set the stage quickly, let's define what we mean by a
2:07
cyber security threat. Essentially, it's any circumstance or event that could potentially harm operations, assets, or
2:13
individuals because an information system gets compromised. You know, unauthorized access, destruction,
2:19
disclosure, modification, or denial of service, that kind of thing. And it's really crucial to remember this
2:24
isn't just about external bad actors, you know, nation states or cyber criminals after money. We absolutely
2:31
have to factor in internal sources, and those tend to fall into two main buckets, right?
2:36
Yeah, that's right. You've got the malicious insiders, people intentionally trying to cause harm, steal data, whatever. But then you have the honestly
2:44
far more common negligent insiders. These are folks who unwittingly cause damage through simple human error, maybe
2:50
poor security practices, or just, you know, clicking the wrong link at the wrong time. So the goal really, regardless of where
2:55
the threat comes from, is protecting the confidentiality, integrity, and availability, the good old CIA triad of
3:02
that information. Indeed. And that protection, it requires continuous yearround vigilance and
3:07
planning. It's not a one-off thing. Which actually brings us to a quick thank you to our sponsors. They provide
3:12
resources that are pretty essential for that kind of strategic defense. We'll be talking a lot about yearround planning
3:18
and humanentric defense today. That's right. Two excellent resources for you are www.scamwatchhq.com.
3:25
They provide timely awareness about seasonal and financial scams. really helps protect your people from those
3:31
tricky social engineering attacks we'll discuss. And also www.cellomarketplace.services.
3:38
That's an invaluable resource for strategic compliance, risk management, and crucially planning those critical
3:43
annual security activities. Yeah, great resources. Links to both are in the description so you can check them out later. Okay, let's get into it.
3:50
Let's unpack this uh this increasingly complex threat landscape starting with the biggest dangers we're seeing in
3:56
2025. Okay, section one, we absolutely have to kick off with the well the
4:02
persistent reign of ransomware. It's the standard nightmare scenario, right? Malware encrypts your critical data.
4:08
Attackers demand payment, usually an untraceable crypto, for the key to get it back, right? And ransomware isn't just a
4:14
volume threat anymore. It's a strategic one because of who it targets. Critical sectors like manufacturing, healthcare,
4:21
critical infrastructure, they're prime targets. But what's really interesting now is how the business model behind it
4:27
has evolved. We're talking about the maturation of ransomware as a service or ray. Race. Yeah. That seems to have
4:33
fundamentally shifted the whole criminal landscape. How exactly does that model make the threat worse in 2025?
4:40
Well, it basically industrializes cyber crime. Think of it like a franchise model. Reyes provides a ready-made toolkit. It
4:47
often comes with customer support, payment processing, even negotiation guides. This massively lowers the
4:52
technical bar for entry. So, we're not just talking about loan hackers anymore. We're talking about networks. Exactly. Fast affiliate networks. These
4:59
affiliates might specialize in different parts of the attack. Some buy initial access from brokers. Remember the KMP
5:04
password example? Brokers find those weak points. Then the affiliate uses the Ryas platform to deploy the actual
5:11
malware and handle the ransom part. This uh this division of labor makes attacks faster, more professional, and way
5:18
harder to trace. And the realworld impact is just terrifyingly effective at stopping operations cold. Take the uh
5:24
the May 2025 interlock ransomware attack on Ketaring Health. They had to cancel
5:30
essential services, surgeries, radiation treatments for almost a week. Mhm. That takes the impact beyond just a
5:36
financial loss, doesn't it? It becomes a direct public safety crisis. Patients are genuinely harmed. Yeah, absolutely.
5:41
Precisely. The cost isn't just the ransom payment, which, let's be honest, often gets paid, or the huge regulatory
5:47
fines. It's the long-term cost. Rebuilding infrastructure, regaining trust, and just the massive operational
5:52
debt from having to revert to like pen and paper for days on end. Okay, so that's the technical threat of
5:58
Ryes. But right alongside it is something arguably more insidious because it targets us humans. Social
6:06
engineering. Ah, yes. Social engineering. Right. The sophisticated manipulation of human trust. It completely bypasses your
6:13
expensive firewalls and defenses. It relies on non-technical means to get access. We're talking standard fishing,
6:19
of course, but also pre-texting, where an attacker makes up a believable scenario, pretending to be someone in
6:24
authority, maybe it support, maybe a vendor, and quidd proquo offering some fake incentive in return for sensitive
6:32
info. And here's where it gets really interesting, right? Because the sophistication in 2025 seems designed
6:37
specifically to beat our best technical defenses, like multiffactor authentication. We're seeing hacker
6:43
groups, scattered spiders, shiny hunters. They're targeting it help desks directly. This is a critical pivot strategically.
6:50
Instead of trying to, you know, crack the MFA token itself, they just call the help desk. They pretend to be a senior
6:56
exec who just lost their phone and desperately needs their MFA reset right now. And they sound convincing
7:01
often. Yes. They use open source intelligence stuff from LinkedIn, company websites to get the victim's
7:06
name, title, maybe even family details. Makes the whole story seem legitimate. And because the IT help desk person has
7:13
legitimate admin access, they become the unwitting key to the kingdom. These attacks are tough because they use
7:19
little or no malware. They're often invisible to your standard endpoint detection. And the impact when they succeed is
7:25
huge. The July 2025 breach at Alliance Life's third party CRM system, that was
7:31
social engineering, wasn't it? It was a perfect example. That single breach potentially compromised data for
7:37
most of their 1.4 million customers in the financial sector, no less. It just shows securing your own network is kind
7:43
of useless if you don't also secure your vendors and address their human vulnerability. Which naturally leads us to the third
7:48
major threat area, insider threats and credential compromise. Whether it's a vendor, a contractor, or a full-time
7:55
employee, having legitimate access is the biggest defense killer. Right? We've already said traditional
8:00
perimeter defenses are useless against insiders, right? Let's dig into that difference between malicious and negligent intent again,
8:07
especially now with hybrid work being so common. Okay. Malicious intent is clear-cut, right?
8:12
Someone wants to steal intellectual property, sabotage systems, commit fraud. Pretty straightforward, though
8:17
hard to detect sometimes. Mhm. But the negligent insiders, they're the real silent killer, especially in these
8:24
hybrid setups. They might use personal insecure devices for work stuff. They might bypass security protocols just
8:29
because it's easier. Or, and this is incredibly common, they use laughably weak or reuse passwords across multiple
8:36
sites. Yeah, that password reuse thing. It's endemic. It is. And the explosion of devices, the
8:41
blurring lines between home and work networks, it just massively increases the attack surface for this kind of
8:47
negligence. And the financial cost of that basic negligence can be extreme. We keep
8:52
coming back to the KMP logistics case because it's so brutal. The Akira ransomware gang didn't need some fancy
8:59
zeroday exploit. They just needed to find one weak password, which is probably easy because as that cyber news
9:05
study of 19 billion passwords showed, 94% were duplicates or reused. 94%.
9:12
That number should honestly send a chill down the spine of every CISO listening right now. 94%. It means that while
9:18
companies spend millions on fancy perimeter defenses, the vast majority of initial access points probably rely on a
9:24
single easily cracked human failing credential reuse. It's an endemic problem and it gives attackers massive
9:31
opportunities for moving laterally once they get that first foothold. Okay, that really sets the stage for this huge growing problem of security
9:38
debt. We know data breaches lead to reputational damage, sometimes even business shutdown. But let's focus on this alarming trend you mentioned, the
9:45
time it takes to actually fix things. Yeah, this is where we shift from the immediate threat like ransomware to a
9:50
more systemic failure within organizations. Our sources show the average time to fix security flaws has
9:56
jumped dramatically. It was around 171 days 5 years ago. Now it's a staggering
10:01
252 days. 252 days. It's what over 8 months. Organizations are knowingly leaving
10:06
high-risk security flaws open for 8 months on average. Yes, that's the average. And half of organizations now carry what's
10:13
called high-risisk security debt. Meaning flaws that have been open for over a year. Over a year. Why is that number climbing
10:19
so fast? Is it just incompetence or is the environment itself becoming just too complex to manage effectively? It's
10:26
probably a mix driven heavily by complexity. First, the shift to hybrid and multi cloud environments creates
10:33
just immense complexity. Flaws are harder to find, harder to isolate, harder to patch across all these
10:38
different systems. Second, organizations are often suffering from tool overload, too many security products, generating
10:45
too many alerts. It leads to alert fatigue, poor prioritization. People just get overwhelmed. They know the
10:51
problem exists, but they lack the clear governance structure or maybe the resources to prioritize and fix it
10:56
efficiently. And the legal consequences for that delay are starting to match the risk. It seems we saw AT&T agree to that huge
11:03
$177 million settlement back in June 2025 following their 2024 breaches. It
11:09
feels like regulators and lawsuits are now directly punishing the duration of the vulnerability exposure, holding that
11:14
252-day average fixed time up as proof of negligence. Absolutely. The longer a known critical
11:20
vulnerability exists, the stronger the case becomes for a regulatory failure, for negligence. The solution to cutting
11:27
down this massive security debt isn't necessarily buying more tools. It's about better governance, better process,
11:33
which leads us neatly into the whole strategic and compliance calendar side of things, which has to be a year- round
11:38
focus. Right? That 252-day figure, that's kind of our northstar for the rest of this
11:43
deep dive, isn't it? It highlights this massive gap between identifying a problem and actually strategically
11:49
resolving it. Speaking of strategy and timely response, let's pivot now into the psychological elements of defense.
11:55
Because all those non-technical attacks, they rely on exploiting human behavior. Yeah. As we move from the firewalls and
12:01
the networks to the human element is fascinating. We see threat actors operating with a well pretty clear
12:06
predictable rhythm. They actually structure their attacks around seasonal patterns. They strike when people are
12:12
distracted, maybe vulnerable, or dealing with high stress things like tax season or the holidays. This is basically the
12:18
operational concept behind what we can call the year round scammer calendar. And since we're closing out October, we
12:25
are deep in that fall winter peak season, which means certain high-risk scams are hitting their stride right
12:31
now. This is exactly why resources like our sponsor www.scamwatchhq.com, at
12:37
scamwatchhq.com which tracks these seasonal trends are so critical for awareness.
12:43
Absolutely. Right now in October we see a few things converging. Yes, you have the sort of fun maybe lower risk
12:48
Halloween costumes, scams, fake online shops trying to grab credit card details, but much more seriously.
12:54
October 15th marks the start of Medicare open enrollment here in the US and that runs through December 7th.
12:59
Okay. Why is that period such a flash point for cyber crime? What's the specific risk there? Well, it targets seniors, right? a
13:05
demographic that's often, though not always, less technically savvy. And it involves high stakes, time-sensitive
13:12
decisions and calls. Scammers poses Medicare reps, insurance agents. They
13:17
use pre-texting to get seniors to verify their personal information. They're after Medicare numbers, social security
13:23
numbers, valuable stuff for identity theft. The urgency created by that enrollment deadline makes people bypass
13:30
their usual caution sometimes. I can see that. And I imagine this human
13:35
centric focus, this pressure only ramps up as we get closer to the actual holiday shopping frenzy in November and
13:42
December. Oh, it explodes. November and December are basically the peak financial season for many cyber criminals. You see the
13:48
massive surge in online shopping scams around Black Friday, Cyber Monday, offering incredible deals that just
13:53
don't exist, purely designed for credential harvesting or stealing payment info. Then you have the fake package delivery scams. Those texts or
14:00
emails impersonating USPS, FedEx, Amazon. Oh yeah, I get this all the time. and your package couldn't be delivered.
14:05
Exactly. Claiming a delivery failed, asking you to click an urgent link to reschedule or pay a tiny redelivery fee.
14:12
It plays directly into people's anxiety about getting their holiday orders on time. And the schemes get more
14:17
emotional, too. We see a spike in holiday charity scams, collecting donations through fake websites or
14:23
social media pages, often after a natural disaster or during major religious holidays. And then there are
14:28
the persistent, really destructive gift card scams. GH those where they demand payment via gift cards.
14:35
Yeah. For fake bills, fake taxes, sometimes even threats, often targeting vulnerable small business owners or
14:41
elderly folks. Gift cards are basically untraceable cash for criminals. Okay, so those are the seasonal peaks.
14:47
But when we look at the financial schemes that cause the most overall damage year round, we have to talk about
14:52
investment fraud, right? The numbers are staggering. Yeah, investment fraud was the single costliest cyber crime in the US in 2024.
15:00
reported losses were over $6.57 billion. Billion dollars with a B. And the
15:05
schemes are getting incredibly sophisticated. They're not just targeting individuals anymore. They're impersonating venture capitalists,
15:11
legitimate financial adviserss, using perfectly cloned investment platforms to build trust before disappearing with the
15:17
funds, affecting businesses, too. Wow. And the scale can be huge. Massive. Remember that case in June
15:24
2025? They dismantled an international network that laundered 460 million. That's nearly half a billion euros
15:30
through crypto exchanges. They deceived over 5,000 victims globally using these clones investment platforms. It shows
15:37
how these operations are global and leverage crypto for speed and anonymity. Okay. And then there's the classic highly targeted attack against
15:43
businesses. Business email compromise or BEC still a major problem. Oh, absolutely. BEC remains a high
15:51
impact fraud. It's where threat actors impersonate a senior executive, maybe the CEO or trusted vendor. They trick an
15:58
employee, usually someone in finance or accounts payable, into making a fraudulent wire transfer or maybe sending sensitive data like employee W2
16:06
forms. Now, interestingly, while the volume of BEC complaint seems to have plateaued a bit, the average cost per
16:12
successful incident keeps rising. It totaled $2.77 billion in losses in 2024
16:18
alone. So, if the average cost is rising, does that mean the attacks that do succeed are more targeted? They're doing more
16:23
homework. Precisely. They might spend weeks inside a compromised executive's email account,
16:29
maybe Microsoft 365. They monitor internal emails. They learn the company's payment approval processes,
16:34
vendor relationships. Then they strike at just the right moment, maybe when the real exec is traveling, creating maximum
16:40
confusion or urgency. The defense here is really non-technical, but it's essential. You have to enforce mandatory
16:47
verbal confirmation using a pre-verified phone number for any change to payment details or wire instructions. period.
16:54
And you need to run regular, highly realistic BEC simulation exercises as part of your ongoing employee training.
17:01
Make them practice spotting these things. Okay, so all these human failures, clicking the fishing link, falling for the pretext call, approving the
17:07
fraudulent wire, they're driven by psychological factors, right? The sources mentioned something called protection motivation theory or PMT. How
17:14
does PMT help explain why people fail to protect themselves or maybe why training sometimes doesn't stick,
17:20
right? PMT is a useful framework here. It helps explain why individuals choose to adopt or more often fail to adopt
17:27
protective behaviors like being cautious online. For someone to be motivated to actually defend themselves, they need
17:34
high scores in two key areas. Threat appraisals and coping appraisals. Okay, let's break that down. Threat
17:40
appraisals first. What's that? Threat appraisals is basically two things. How severe you think a potential
17:47
cyber event would be and how vulnerable you personally feel to it. So if an employee thinks fishing is something
17:52
that only happens to other people or maybe they think a data breach is just an IT problem, their threat appraisal is
17:58
low. They don't see the personal risk. So they're not motivated to change their behavior. Okay. So I need to understand the danger
18:05
and feel like it applies to me. But even if I get that, it doesn't mean I know what to do about it or if it will even
18:11
work. Right. Exactly. That's the second critical piece. Coping appraisals. This has two
18:17
parts as well. First is self-efficacy. That's your confidence in your own ability to successfully perform a
18:23
security action like spotting a really convincing spear fishing email. Second is response efficacy. Your belief that
18:31
the protective action you take like reporting the email will actually work and make a difference.
18:36
Ah okay. So if a company gives its employees like confusing oneoff annual
18:42
training then employees likely feel low self-efficacy, right? They don't trust their own ability to spot the scam. They
18:48
might also feel like reporting it is pointless, low response efficacy. So what happens? They often revert to
18:54
apathy. Just click delete or worse, click the link. This is why lack of awareness, lack of understanding their
19:00
personal role, and inadequate education are so often cited as key failures in overall risk management.
19:05
So fundamentally, the human isn't the weakest link because they're inherently flawed, but often because the organization fails to properly boost
19:12
those coping appraisals. It needs continuous relevant training and clear support. Precisely. It's really an
19:18
organizational failure as much as a personal one. Effective information security management systems in ISMS, they require moving way beyond that
19:24
single check the box annual training video. Training needs to be continuous, role-based, context specific, and
19:31
visibly supported by senior management to really overcome that user apathy and turn employees into active participants
19:36
in the company's defense. Okay, that transition from apathy to active strategic defense brings us
19:42
perfectly into our next section. We need to move beyond just reacting to threats and start focusing on strategic
19:47
architecture, compliance, and preparing for what's next. Particularly the AI revolution heading into 2026. Right,
19:54
since we are in Q4, the last quarter of the year, October isn't just about cyber security awareness month activities.
20:00
It's crunch time for strategic planning, too. Organizations have to demonstrate their security posture through
20:05
compliance activities, and these happen year round. It's a constant cycle. Now, if you're managing this complex
20:10
calendar, you know how vital structured planning is, which brings us back to our sponsor, www.cizoarketplace.services.
20:18
Their resources are specifically designed to help CISOs navigate this exact annual roadmap. Yeah, looking at that typical annual
20:24
compliance calendar. October is intense. You've got quarterly KPI reviews wrapping up. You're finishing off
20:30
awareness month activities and there's a huge deadline looming. The annual ISO 2701.202
20:37
202 transition deadline is October 31st. That's a big one for many orgs. Plus,
20:43
organizations dealing with the US defense industrial base, the DIB, are often doing their annual CMMC reviews
20:48
around now. And critically, this is when serious drafting begins for the next year's security strategy, usually
20:54
finalized in December. Okay, we talked about that average fixed time for security debt being 252 days.
20:59
If a company is struggling with that kind of internal lag, how incredibly difficult must it be to meet a hard deadline like that October 31st ISO
21:06
transition, which really demands comprehensive governance, right? Oh, it's almost impossible. ISO 27,0001
21:12
is, you know, the global gold standard for an information security management system, an ISMS. It forces you to have
21:18
documented processes for everything. Governance, risk treatment, access control, incident response, the works.
21:26
If you're sitting on eight months or even over a year of unresolved high-risisk security debt, you
21:32
fundamentally lack the demonstrated structure and the documented evidence required for successful ISO transition
21:37
or certification renewal. So the compliance frameworks like ISO or maybe NIST CSF. They almost act as the
21:44
mechanism forcing organizations to attack that 252day fix time. In a way, yes, they provide the
21:50
structure and the deadlines. They mandate things like annual risk assessments often done in January and require external penetration testing
21:56
maybe scheduled for March. These aren't just bureaucratic hoops. They're forcing functions for strategic hygiene and
22:02
continuous improvement. Okay, that's a great point about compliance driving action. Now, let's talk about the huge force multiplier
22:07
that's redefining both compliance and defense, the AI arms race. Ah, AI. Yeah, the ultimate double-edged
22:14
sword right now in cyber security. On the offensive side, attackers are absolutely using generative AI to
22:19
automate scale and speed. This means automating the creation of custom, highly realistic social engineering
22:25
messages. Think hyperpersonalized fishing emails at a volume that was just unthinkable a couple of years ago. Even
22:32
worse, AI is powering polymorphic malware. That's malware that can automatically change its own code
22:37
structure to evade signaturebased detection systems. It makes attacks much faster and way harder for traditional
22:43
defenses to catch. That speed is genuinely frightening, especially when you measure it against
22:49
our 252-day average fix window. It feels like the offense is accelerating way faster than the defense can patch. But
22:56
on the flip side, the defense side is also investing heavily in AI, right? Where are US businesses seeing the most
23:01
benefit from defensive AI? Defensive AI is rapidly becoming foundational to the modern security
23:06
operations center, the SOC. Its biggest strength is processing power. AI can
23:12
analyze literally billions of security events daily, something no human team could ever handle to find those subtle
23:19
anomalous patterns that might indicate a breach or an emerging vulnerability. It dramatically speeds up incident
23:25
response by automating the initial data gathering, triage, and alerting processes. Get the right info to the
23:31
human analyst faster. And crucially, it's helping with vulnerability management through AI powered code
23:37
scanning, identifying security issues in the code itself in real time. ideally before it ever gets deployed.
23:42
Okay, but integrating these powerful tools isn't without risk itself, is it? There's this challenge people are
23:47
calling shadow AI. Yes, shadow AI is a huge emerging risk. It refers to the ungoverned, unapproved
23:53
use of external general purpose AI tools by employees. Think about staff uploading proprietary company documents
23:59
into a public large language model like Chat GPT or others, maybe to summarize meeting notes or debug internal code
24:05
snippets. Ooh, yeah, that sounds bad. What are the risks there? Massive compliance risks for starters, especially under
24:12
regulations like GDPR in Europe or the upcoming EU AI act. You're potentially exposing sensitive
24:18
data, significant data exposure risk in general, and potentially catastrophic intellectual property concerns. By
24:24
feeding your proprietary data into an external LLM, you are inadvertently training that external model with your
24:31
company's most sensitive information. It's gone. So the answer isn't necessarily to just ban all AI tools,
24:38
right? It's more about putting guard rails in place. Exactly. It demands a policy first approach. Organizations need clear
24:44
policies on acceptable AI use, approved tool lists, and extensive employee education on how to use these tools
24:50
safely, especially regarding data handling. And you need technical controls, too. Maybe things like application proxies or data loss
24:56
prevention tools configured to monitor and potentially block unauthorized data transfers to external AI services. You
25:02
have to govern the usage before it becomes a massive liability. Okay. So to combat these faster AI
25:08
powered threats and manage all this resulting complexity, the fundamental network architecture itself has to
25:14
change. The principle everyone talks about now is zero trust architecture or ZTA. It seems non-negotiable.
25:20
It really is becoming the baseline expectation. ZTA is often called perimeterless security. Its core
25:27
principle is simple but powerful. Never trust. Always verify. You start from the
25:32
assumption that your network could already be compromised. This means you never trust users or devices by default,
25:37
even if they are physically inside your corporate network or have been previously verified. Every access attempt needs revalidation.
25:44
How does that work in practice? What gets verified? It requires continuous identity verification, often using strong MFA. It
25:51
requires checking device compliance. Is the device patched? Running approved security software. And it rigidly
25:56
enforces the principle of lease privilege access. Users only get access to the specific resources they
26:01
explicitly need for their current task for the minimum time necessary. Access is granted per request, not based on
26:08
just being on the network. Okay, let's drill down into a concept that builds on that. Zero trust data or
26:13
ZTD. Applying zerorust principles directly to data access itself. How does
26:18
that work and why is it better than just traditional role-based access? Yeah, ZTD is critical for managing data
26:24
in modern complex environments. Think multicloud data links, sensitive
26:30
customer databases, and it's vital for meeting granular privacy regulations. Instead of trusting a user simply
26:35
because they have a certain job title or belong to a certain group, that's role-based access control or RBAC, zero
26:42
trust data often relies on attribute-based access control or ABAC. Okay, ABAC attributes like what?
26:48
ABAC applies access policies based on a dynamic combination of attributes related to the user, the data, and the
26:54
context. attributes could include the sensitivity classification of the data itself, the user's verified identity and
27:00
role, their current physical location or they in the office or remote, the time of day, the security posture of their
27:05
device, maybe even their required clearance level for that specific data type. So an AB8 policy might be
27:11
something like allow access to project Phoenix documents only if the user is authenticated via MFA is connecting from
27:18
a corporate managed device located within North America and it's during standard business hours regardless of
27:24
their job title. Precisely. It's dynamic contextaware real-time access governance applied
27:29
right at the data layer. Now ABAC is definitely more complex to set up and manage compared to simpler RBAC roles.
27:35
But for many organizations, especially those handling sensitive data across hybrid environments, it's becoming the
27:41
only way to effectively combat data sprawl, truly enforce least privilege for data, and ensure the kind of privacy
27:47
preserving design required by new mandates like the EU AI act or GDPR. And this push towards ABAC and ZTD, it
27:55
feels like part of a bigger shift towards embedding security earlier. The idea of secure by design.
28:00
Exactly. Secure by design is transitioning rapidly from just being a best practice recommendation to becoming
28:07
a business and regulatory requirement likely solidified by 2026. What it means fundamentally is
28:13
prioritizing customer security and privacy as a core business requirement right from the start. You build security
28:19
into the product development life cycle from day one. Often called shifting left in the development process. Instead of
28:25
trying to bolt on security fixes 252 days after deployment, you use things like threat modeling, secure coding
28:32
practices, maybe those AI powered code scanners we mentioned, and established security frameworks like the CIS
28:38
controls or NIST CFF 2.0 to ensure vulnerabilities ideally never make it into production in the first place.
28:44
So security isn't an afterthought or a separate phase anymore. It has to be part of the operational DNA of the
28:49
organization. That's the goal. Needs to be baked in, not sprinkled on later. Okay, strategic
28:56
year-round compliance architectural overhaul with ZTA and ZTD integrating AI
29:01
defensively. That covers a lot of the internal network and data strategy. But what about the physical infrastructure
29:08
that actually keeps our modern society running the critical systems, right? The security of critical national
29:13
infrastructure or CNI is arguably the highest stakes area we need to discuss. We're talking about power stations,
29:19
water treatment facilities, transportation networks, health systems, the things society depends on.
29:24
Historically, these industrial control systems, the ICS that run these facilities were protected mainly by
29:29
physical isolation. They were airgapped, meaning not connected to the public internet or even corporate IT networks.
29:35
But that's changed, hasn't it? the drive for efficiency, remote management, real time data. It means these systems are
29:42
increasingly connected now, which is great for operators maybe, but potentially terrible for security.
29:48
Exactly. That connectivity opens them up to cyber attacks they were never designed to withstand. And securing
29:54
these operational technology or OT environments is uniquely challenging. ICS systems often contain legacy devices
30:02
that might be decades old running outdated software that can't easily be patched. They use specialized OK
30:08
protocols that IT security tools often don't understand. And crucially, the cost and operational disruption of
30:14
taking these systems offline for upgrades or patching can be prohibitive. You can't just reboot a power grid
30:20
component during peak demand without risking serious consequences. Production downtime is a massive concern. Okay. So
30:26
given those significant constraints, where is the strategic focus for improving security particularly for
30:32
something like the power grid? What can be done? The focus is shifting towards increasing situational awareness and resilience
30:38
without disrupting the physical operations if possible. This requires multistakeholder risk approaches
30:43
involving engineers, IT security, physical security regulators. And a key development is the use of hybrid cyber
30:49
platforms. Think of these as sophisticated digital twins. digital twins like a virtual copy
30:55
essentially. Yes. They replicate the physical OT environment, the control systems, the networks, the data flows in
31:01
a safe, isolated virtual space. This allowed organizations to do things they could never do on the live system. They
31:08
can safely test how attacker tactics, techniques, and procedures TTPs might work against their specific setup. It
31:15
can conduct realistic penetration testing, practice incident response drills, validate defenses, all without
31:20
risking a real world blackout or disruption. That makes sense for testing. But what about deploying new technologies like AI
31:26
directly into these highly sensitive realworld OT environments? We need speed, sure, but failure there is
31:33
potentially catastrophic. How do you balance that? That is the critical question. And the approach here emphasizes what's often
31:39
called assistive artificial intelligence or AI and maintaining a human in the
31:45
loop paradigm. AI solutions are designed to aid human operators, not replace them
31:50
entirely in critical decision-making. AI can automate routine tasks like log
31:55
analysis and monitoring, identifying anomalies much faster than humans can. It can be trained on the unique
32:01
proprietary data models specific to that organization's ICS or SCADA systems. But and this is crucial, we generally avoid
32:08
full automation of the response actions in critical infrastructure. The regulatory hurdles are high and the
32:14
potential for a cascading physical failures from a bad automated decision is just too great. So the AI might suggest the fix or the
32:21
response, but a trained human operator has to confirm and execute the action. Exactly. Human oversight remains
32:27
essential for reliability and trust in these environments. The paradigm is human empowerment through AI, not human
32:33
replacement. And architecturally this needs structure, right? The sources mentioned the Purdue model integrated
32:39
with an industrial edge computing platform. How does that help? The Purdue model is a standard way to conceptualize and segment the different
32:46
layers within an industrial control environment. It goes from the physical sensors and actuators at the lowest
32:51
level, level zero, up through the control systems, level one, two, the supervisory systems level three, and
32:57
finally to the enterprise IT network, level four, five at the top. Integrating an industrial edge computing platform
33:03
means placing computing power and analytics capabilities closer to the source down near levels one and two at
33:09
the edge of the OT network. This allows for real-time monitoring and processing of operational data right where it's
33:15
generated before it even hits the wider network. This segmentation and localized processing provide much more granular
33:22
datadriven situational awareness. It helps defenders potentially predict or isolate threats based on subtle
33:28
deviations in the physical process data itself. Okay, that covers domestic critical infrastructure, but the conversation has
33:35
definitely gone global, escalating into concerns about cyber warfare and geopolitical threats, particularly
33:40
affecting the defense industrial base, the DIB. Oh, absolutely. Nation state actors are increasingly using sophisticated cyber
33:47
capabilities as tools of statecraft. We see espionage targeting defense secrets, disruptive attacks like wiper malware
33:54
designed to destroy data, state sponsored ransomware groups used for plausible deniability or revenue
33:59
generation, and coordinated disinformation campaigns aimed at undermining trust or influencing
34:04
populations. This clear escalation necessitated a massive push by the US Department of Defense to shore up the
34:11
cyber security of its vast supply chain, the defense industrial base. And that protection mechanism is the cyber
34:16
security m maturity model certification CMMC 2.0. What does CMMC actually mean for the what 300,000 or so contractors
34:23
in the DIB? CMMC 2.0 is a fundamental gamechanger for the DIB. It moves cyber security
34:30
requirements from being largely voluntary guidance based on NIST standards to being a mandatory
34:35
contractual requirement. It enforces tiered cyber security levels level one for basic safeguarding of federal
34:41
contract information FCI up to level three for protecting sensitive controlled unclassified information CUI.
34:49
And crucially for levels two and three it generally requires independent thirdparty assessments conducted by
34:54
accredited certified thirdparty assessor organizations or C3PAOs.
35:00
No more self addestation for the critical stuff. So basically, if you handle sensitive government information,
35:05
your cyber security posture, as verified by an outside auditor, directly determines your ability to win and keep
35:11
lucrative federal defense contracts. That's the bottom line. Your security level becomes a condition of doing business with the DoD.
35:17
What's the biggest challenge this poses, especially for the smaller subcontractors in the DIB? It sounds expensive and complex.
35:22
Yeah, the burden is immense. No question. Both bureaucratically in terms of documentation and process and
35:28
financially. CMMC level one maps to basic NIST requirements which most should be doing anyway. But level three
35:35
required for handling CUI involves implementing a much larger set of stringent controls derived from NIST
35:40
SP800171. Many small and medium-sized subcontractors simply lack the internal
35:46
cyber security expertise and frankly the capital needed to implement all those controls and pay for the mandatory third
35:52
party audits. It forces a massive investment in security hygiene. For some, it might mean choosing between
35:57
achieving full compliance or potentially losing their eligibility for federal contracts.
36:03
It's tough, but from the DoD's perspective, it's viewed as non-negotiable for protecting national security information flowing through the
36:09
supply chain. Okay, so CMMC is hardening the domestic DIP. Finally, let's zoom out one last
36:15
time and look at CISA's global strategy. CISA being the US Cyber Security and Infrastructure Security Agency. How does
36:22
their plan guide US businesses and their international partners? Right. CISA's overall cyber security
36:27
strategic plan lays out three big enduring goals for the domestic ecosystem. Goal one, address immediate
36:34
threats. Basically, make it operationally harder and more costly for adversaries to succeed right now. Goal
36:40
two, harden the terrain. This is about promoting strong, often mandatory security practices across the board.
36:46
Think critical infrastructure standards, pushing secure by design. And goal three, drive security at scale. This
36:53
involves fundamentally shifting the market, prioritizing security as a basic safety issue for all technology providers, making security a default
37:00
expectation, not an optional extra. Okay, that's the domestic focus. But globally, we know US critical
37:05
infrastructure relies heavily on foreign infrastructure too. Supply chains, communications links. Absolutely. And CISA's FY2025 2026
37:13
international strategic plan explicitly recognizes this deep interdependence. Their three main international goals
37:19
reflect this. First, bolster the resilience of foreign infrastructure on which the US directly depends. Helping
37:25
key allies secure their critical systems benefits everyone. Second, strengthen integrated cyber defense. This involves
37:31
maturing bilateral and multilateral partnerships, especially between national computer security incident response teams or seerts.
37:38
What exactly do those seesert engagements achieve? Is it just general threat intel sharing? It's often much
37:44
more rapid and operational than just general intel sharing. Seeserts are designed for highly technical
37:50
nearrealtime information exchange about specific vulnerabilities being exploited, active attacker TTPs,
37:56
indicators of compromise like malicious IP addresses or file hashes during an
38:02
ongoing incident. This collaboration speeds up the collective defense across borders. If one country sees a new
38:08
attack technique, they can quickly warn partners so they can block it, too. And CISA's third international goal is
38:13
simply to unify agency coordination of all these various international cyber security activities, ensuring the US
38:19
government presents a coherent front. And the ultimate aim seems to be driving global standards upward, encouraging
38:25
partners everywhere to adopt things like secure by design principles using software bills of materials, esbombs.
38:31
It's exactly esbombs. Those detailed lists of all the software components within a product help manage supply
38:37
chain risk. CISA is also pushing for secure AI system development globally. The idea is that raising the security
38:44
baseline everywhere reduces the collective risk for everyone. It really is an ecosystemwide challenge that
38:49
demands international cooperation. # tagoutro. Okay, so let's try to wrap
38:54
this up. To summarize what we've really unpacked today as we close out October and look towards 2026, the key takeaway
39:00
is that the adversary is faster, more automated. They're using rays models and generative AI to scale sophisticated
39:06
attacks. Think polymorphic malware that evades detection and hyperrealistic social engineering that's harder than
39:11
ever to spot. Right? And defending against this isn't about just one silver bullet. It requires a fundamental architectural
39:18
shift. Zero trust has to become the default security posture and that needs to extend down to zero trust data using
39:25
mechanisms like ABAC for granular control. This technical shift has to be married with strict yearround adherence
39:32
to compliance frameworks whether it's ISO 2701 NIST CSF or CMMC 2.0 for the
39:38
DIB. These frameworks force the strategic hygiene needed to combat that growing 252day security debt we talked
39:45
about. And critically the mindset needs to shift too. Leading organizations are starting to view cyber security spending
39:51
not just as a necessary cost or a burden but as a strategic investment. an investment that yields tangible business
39:57
benefits like winning contracts in regulated sectors like the DIIB, potentially getting lower cyber insurance premiums, and of course, the
40:03
massive cost avoidance from preventing major incidents in the first place. Yeah, the path forward seems to require this balance, doesn't it? balancing
40:10
innovative leadership like adopting assist of AI carefully in critical infrastructure with sophisticated
40:15
disciplined risk management and always always remembering that the investment in your people through continuous
40:21
effective training that boosts those coping appraisals we discussed has to keep pace with the investment in shiny
40:26
new technology couldn't agree more people process and technology okay so here is the final provocative
40:33
thought for you our listener to carry forward it ties directly back to that urgency created by the AIA page, we
40:40
established that the average fixed time for known security flaws is now a staggering 252 days. Given the
40:47
incredible speed at which AI can now generate adaptive malware and conduct automated massive scale fishing
40:52
campaigns, the critical question for every single organization shifting towards a 2026 mindset isn't just if
40:58
you'll be attacked. It's whether your response velocity, your ability to detect, react, and remediate can
41:04
actually beat the sheer accelerating speed of the automated adversary. How quickly can your organization
41:09
realistically shorten that 252-day window? That time compression, shrinking that window, that's really the 2026
41:16
imperative. And for strategic planning resources, including those compliance calendars and framework road mapaps that
41:22
are essential for helping you shrink that window. Definitely visit our sponsor www.comarketplace.services.
41:28
And to help you stay ahead of those human- ccentric seasonal scams that target your people and make them vulnerable, especially those Medicare
41:35
and holiday scams that are peaking right now, make sure you check out the timely alerts and resources over at www.scamwatchhq.com.
41:43
Thanks for joining us for this deep dive.